Table of contents
Table of contents
As an organization or individual doing social good, it may seem like you’re not on the radar of cybercriminals. After all, these bad actors tend to strike well-known Fortune 500 companies and for-profit businesses. Companies like Facebook, Yahoo, Adobe, Equifax, Quora, and Canva have all been victims of massive data breaches in recent years.
But the Blackbaud data breach proved that this couldn’t be further from the truth. In 2020, more than 120 nonprofits using Blackbaud’s fundraising platform and services learned their sensitive data was stolen and held hostage in a ransomware attack. Millions of donors, customers, patients, and staffers were affected, and the attack went on to become the largest healthcare data breach of 2020.
Now more than ever, nonprofits need to understand how to protect themselves and their supporters.
We’re here to help. In this article, we’ll examine the Blackbaud data breach as a cautionary tale, discuss the rise of cyberattacks on nonprofits, and give you five practical ways to shield your organization from future data breaches.
The Blackbaud data breach: What happened?
Blackbaud is a South Carolina-based software company and one of the largest nonprofit technology companies, which made the breach big news. With a mission to help social good companies do more, Blackbaud provides tools like Raiser’s Edge fundraising software and CRM systems, marketing tools, financial support, and more.
In May 2020, Blackbaud’s cybersecurity team discovered that a ransomware attack had been in progress since February 2020. In this type of cyberattack, criminals steal important data to prevent the organization from being able to operate as usual. There are two common scenarios:
- Scenario 1: Cybercriminals infiltrate your system and encrypt sensitive information — like email addresses, medical history, bank account details, or trade secrets. They turn your data into a code that your team can’t decipher.
- Scenario 2: Cybercriminals infiltrate your system and make a copy of your sensitive information and threaten to publish or sell it to other criminals, competitors, or countries on the dark web.
The attackers make a ransom demand, usually for money or cryptocurrency like Bitcoin. In return, they promise to unencrypt the original data or permanently destroy the copied data. Note the word “promise.” Sometimes, even when the victim pays, ransomware groups still sell the data.
Blackbaud’s response to the data breach 💬
Once they identified the attack, Blackbaud’s Cyber Security team partnered with forensics experts and law enforcement. They stopped the ransomware group from encrypting their data (i.e., Scenario 1) and kicked them out of their system. However, the criminals managed to make a copy of a subset of data before they were removed (i.e., Scenario 2), and demanded a ransom to delete the stolen data.
Blackbaud decided to pay the ransom, and the cyberattackers assured their team that all their copies were permanently destroyed. Blackbaud also hired experts to monitor the dark web in case the information was sold, but said they haven’t seen any evidence to suggest it.
Fallout from the Blackbaud data breach 💥
In July 2020, Blackbaud first notified customers of the breach. Although the company stopped part of the ransomware attack, many Blackbaud users were upset. The biggest criticism was that the attack began in February, wasn’t detected until mid-May, and users weren’t notified until July.
At first, Blackbaud claimed that bank account information, Social Security numbers, usernames, and passwords weren’t compromised, but later reversed this. As of February 2021, Blackbaud is facing more than 20 lawsuits and class action cases over the breach.
Nonprofits have called Blackbaud “negligent” and claimed they violated the Health Insurance Portability and Accountability Act (HIPAA), California Consumer Privacy Act, and General Data Protection Regulations (GDPR) in Europe.
Who was affected by the cyberattack?
The ransomware group targeted a wide range of nonprofit organizations, both in the U.S. and internationally, including the following:
- Healthcare organizations
- Charities
- Human rights organizations
- Universities and colleges
- Churches
- Food banks
- Trusts for historical buildings
- Nonprofit radio stations
(If you’re wondering if any of your data was compromised, you should have received word by now.) Some of the most well-known names in the attack include Planned Parenthood, Human Rights Watch, Boy Scouts of America, the George W. Bush Presidential Center, and the Rhode Island School of Design.
Estimates put the number of victims at over 10 million individuals. They’re mostly users, members, patients, donors, volunteers, prospects, and employees of the nonprofits.
What information was stolen?
During the roughly four months that cybercriminals had access to Blackbaud’s system, they accessed a variety of personal data. This included:
- Full names
- Dates of birth
- Phone numbers
- Mailing addresses
- Email addresses
- Donation history (amounts, dates, etc.)
Then, in September 2020, Blackbaud told a smaller group of customers that more of their data may have been stolen, including:
- Social Security numbers
- Bank account information
- Credit card information
- Usernames
- Passwords
In the hands of criminals, this personal data makes supporters vulnerable to identity theft.
It also leaves them wide open for phishing attempts, when a criminal sends a message that looks like it’s from a legitimate person or business and asks them to do something, like update their personal information, click on a virus-infected attachment, or send money.
Why nonprofits are increasingly at risk for cyberattacks
Cybercriminals thrive on chaos and confusion, and there was no shortage of that during the height of the COVID-19 pandemic. Ransomware attacks were especially effective. According to a CrowdStrike survey, six in 10 organizations suffered a ransomware attack in 2020.
Many nonprofits are dealing with fewer donations and revenue struggles due to COVID while still trying to fulfill their missions. That means investing in cybersecurity is low on the priority list, which raises the risk of cyberattacks. Victims may be more likely to pay the ransom so they’re able to fundraise and serve their community.
In addition, the quick shift to remote work and digital fundraising has many nonprofit teams using some software tools for the very first time. If they aren’t trained in cybersecurity best practices (like strong passwords or safe email usage) each account and device acts like a weak link in the chain.
The Blackbaud incident shows how one bad actor can put millions of people — including your amazing clients and supporters — at risk. A data breach can also lead to downtime, loss of customers, reputational damage, and legal troubles.
But it’s not all doom and gloom. Let’s look at ways to stay one step ahead of cybercriminals.
5 cybersecurity measures to prevent and prepare for data breaches
The best defense is prevention.
Below, we’ll cover a combination of internal and external cybersecurity tactics to protect your organization’s data. Unfortunately, not every cyberattack is preventable, but you can limit the damage with these steps.
1. Choose a secure fundraising platform 💻
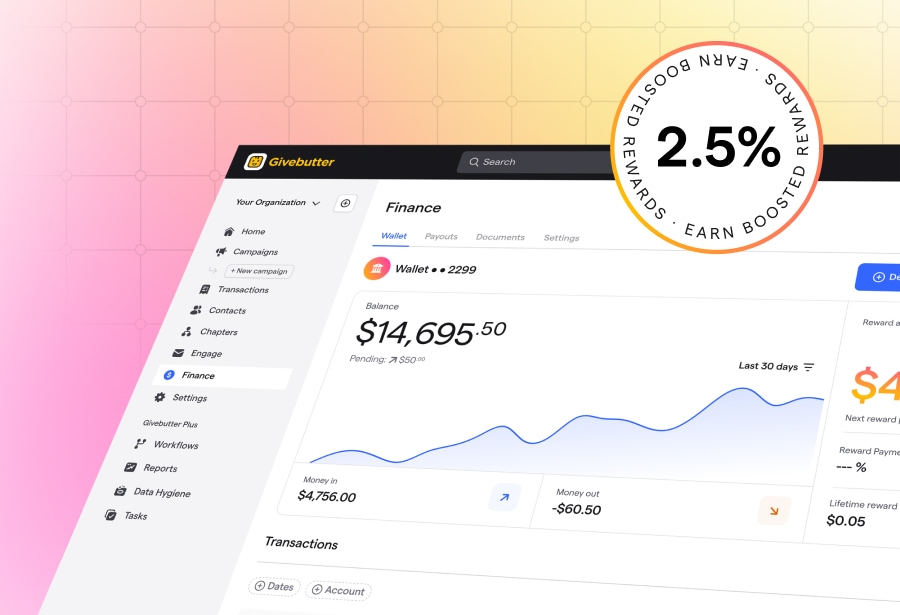
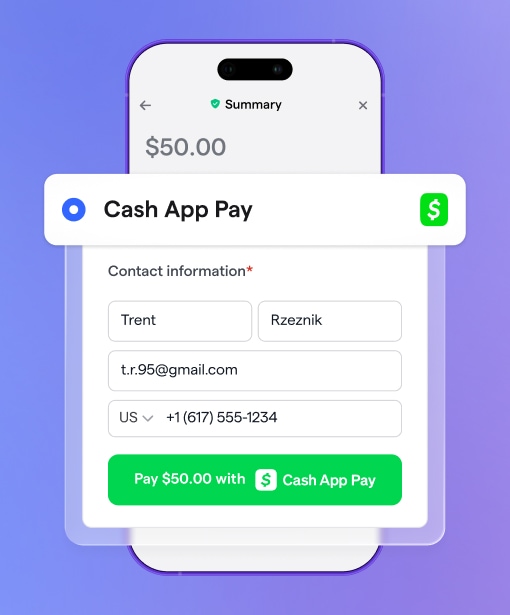
Start at the source! At a minimum, make sure your fundraising platform uses payment encryption technology (Givebutter uses the very best) and stays up-to-date with technology regulations and advances.
Don’t be afraid to ask questions when you’re evaluating a new platform. Is your data automatically backed up in multiple locations? Do they have a plan for different security incidents? What technical support is available? Are your donations protected?
2. Outsource your cybersecurity needs 👥
Often, it’s best to leave it to the experts. Consider hiring an on-site or virtual cybersecurity team that specializes in nonprofits. They can research, test, and use cutting-edge technology solutions to keep your organization secure.
If you already have an IT consultant or department, get their feedback. Do they feel they have all the resources they need to protect your organization from data security risks?
3. Schedule regular cybersecurity risk assessments ⏰
A cybersecurity risk assessment is like an annual check-up for your nonprofit. It’s usually performed by IT staff or security firms and clues you into any weaknesses in your network, software (like your fundraising platform), or devices.
It’s the perfect way to head off security threats, but only 30% of nonprofits have run one before. If you’re looking for an immediate way to boost your security, a cybersecurity risk assessment is the place to start.
4. Have guidelines and protocols in place 📔
Are you part of the 80% of nonprofits that don’t have a policy to address cyberattacks? Every organization needs to create a clear, specific plan for how they’ll respond in these stressful, fast-moving situations. Instead of wondering what to do, your team can act quickly and effectively, limiting fallout and maintaining the trust of your supporters.
Not sure how to approach this? This is another great opportunity to consult with a cybersecurity team and come up with guidelines specific to your needs.
5. Train your employees on safe usage 👍
Can your employees recognize the difference between a real and fake email from their co-workers? Do they know how to create strong, unique passwords?
Employee awareness and training is essential to reducing risk. Even the savviest tech wizards need to brush up on cybersecurity best practices every year, especially if you’re in a high-risk industry like healthcare. You can outsource this to an IT team or search for courses online like this Security 101 training.
A more secure future
As nonprofit operations increasingly move online, relying on technology can sometimes feel a little like this:
However, the biggest cybersecurity risk your nonprofit faces is thinking that a cyberattack can’t happen to you. As the Blackbaud data breach showed, cyberattacks can and do happen, whether criminals directly target your organization or go after the websites, tools, and partners you use.
Fortunately, there are many simple, protective measures you can utilize to lower the chance of attacks and make them less effective. You’re on your way! We’ve covered the most important steps in this article: Pick a secure fundraising platform, consult the experts, set up cybersecurity risk assessments, train your employees, and have a response plan.
.svg)




%20(1).png)



.svg)